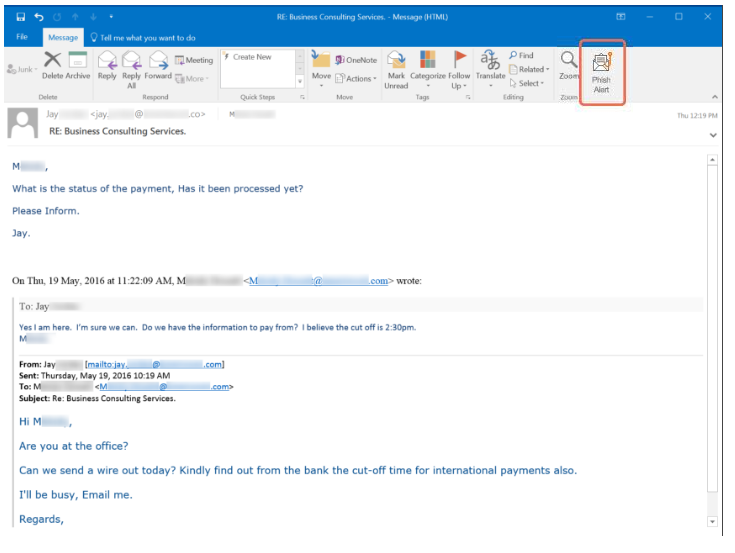
Court Rules Social Engineering Scam Not Covered Under Bank's Forgery and Unauthorized-Signatures Policies | Case Study | Goldberg Segalla

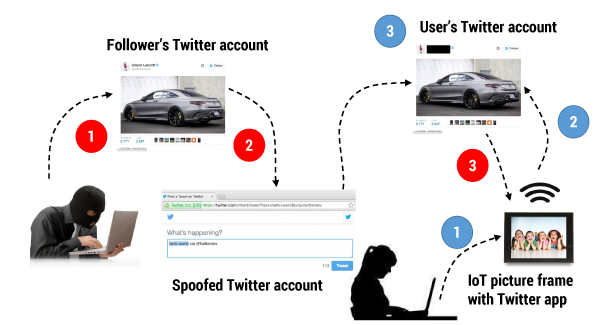
Comparing Misuse Case and Mal-Activity Diagrams for Modelling Social Engineering Attacks: Computer Science & IT Journal Article | IGI Global

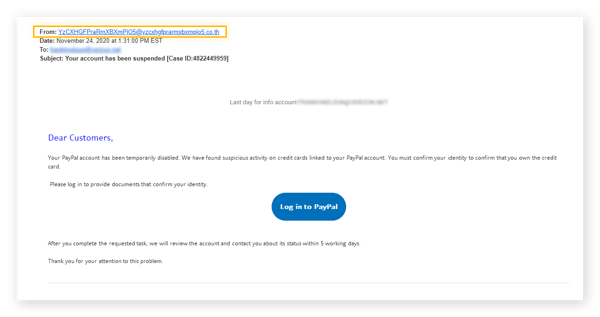
Social Engineering Attacks: A Look at Social Engineering Examples in Action - Hashed Out by The SSL Store™